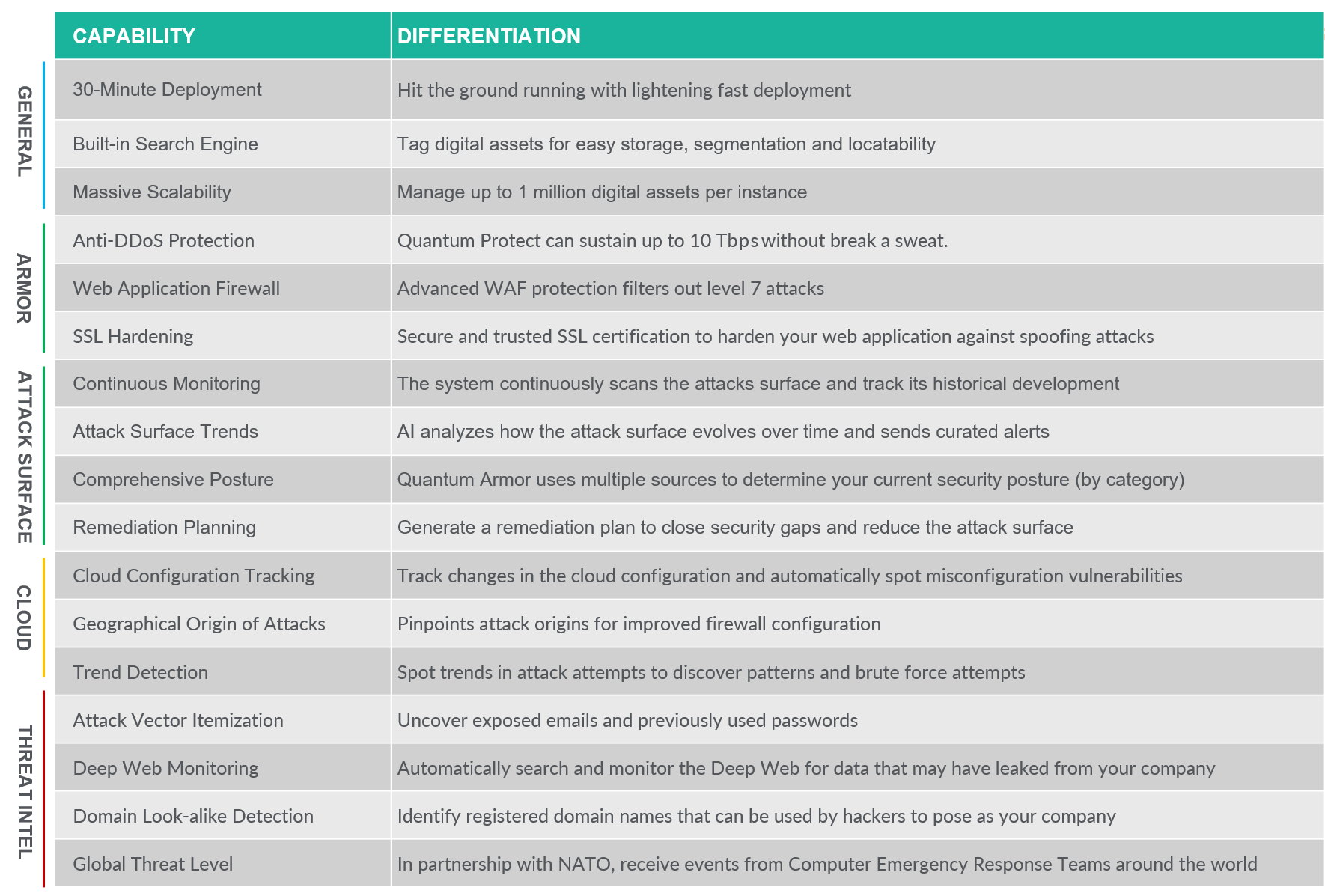
Quantum Armor combines EASM and DRPS to understand your real-world risks
from the outside-in, prioritize your mitigation efforts, and automate your security reporting.
See beyond your perimeter with continuous asset cataloging, IP detection and shadow IT discovery.
Quantum Armor combines the range of an EASM platform with the depth of cutting-edge DRPS.

Correlate your assets and vulnerabilities to produce actionable risk assessments.
Our LLM ingests thousands of data points to provide clear security briefs to secure your company.
Our attack surface monitoring system doesn't require any software or agents to be installed on-target. Quantum Armor gathers information that is externally available to rate the cyber security posture of your digital assets.
Learn More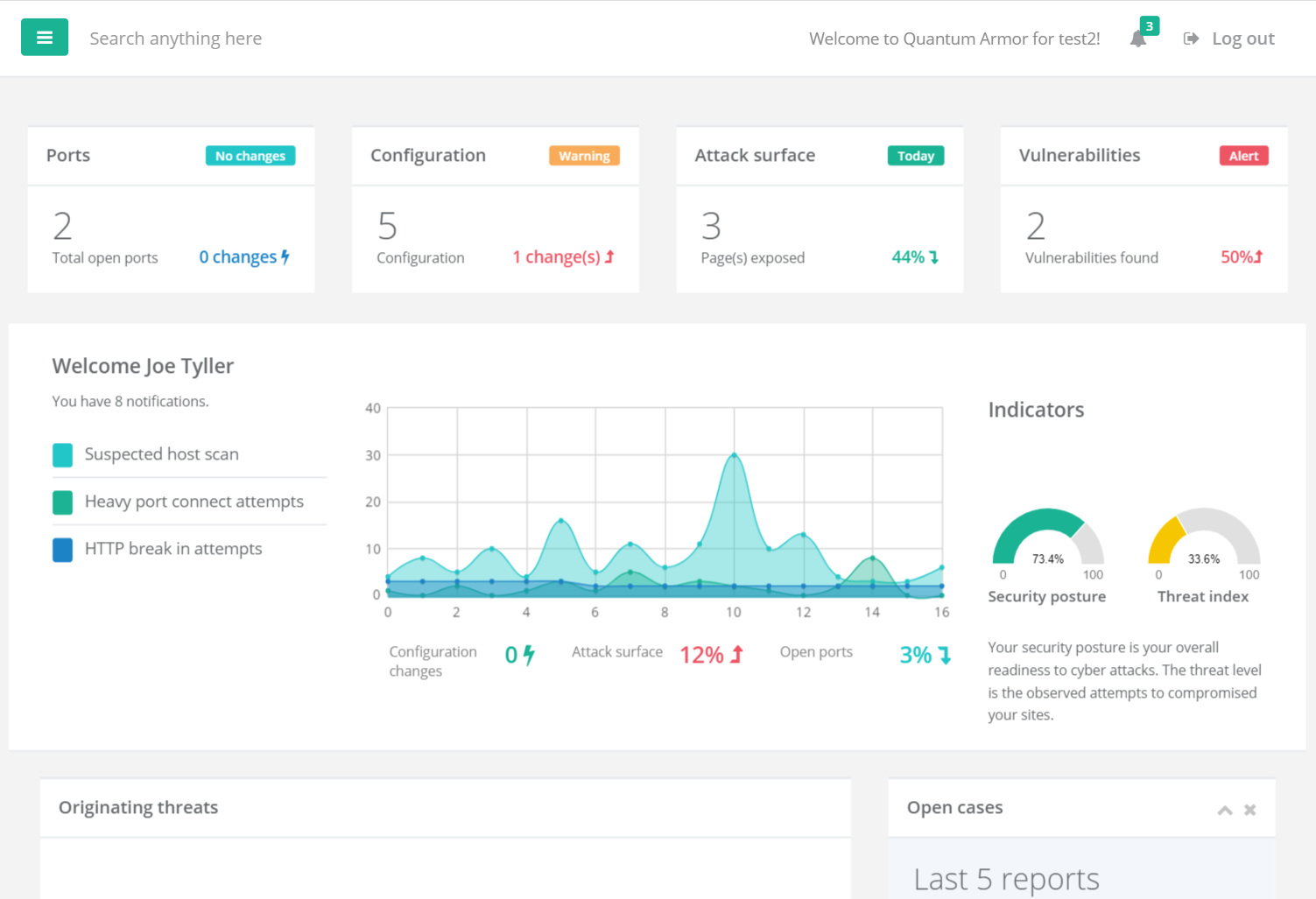
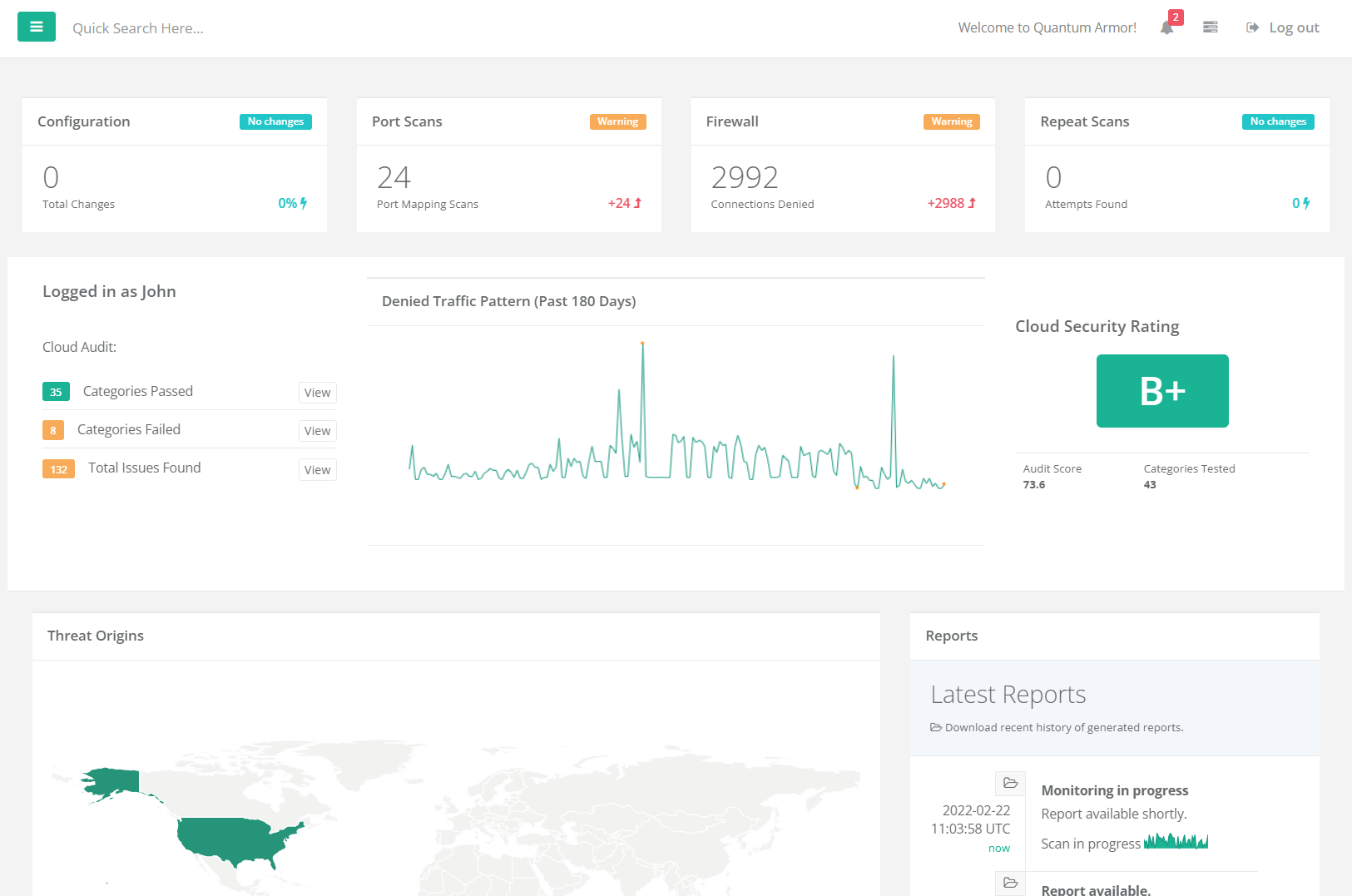
Utilizing a range of proprietary algorithms, Quantum Armor helps you monitor, audit, and harden your cloud instance without installing any agents. This is done by leveraging the APIs that are already in place and provided by the cloud vendors themselves.
Learn MoreBy partnering with NATO, Quantum Armor is capable of identifying key IoCs, malware strains and threat actors operating across the web, and then cross-reference those against your organization's logs and data.
Learn More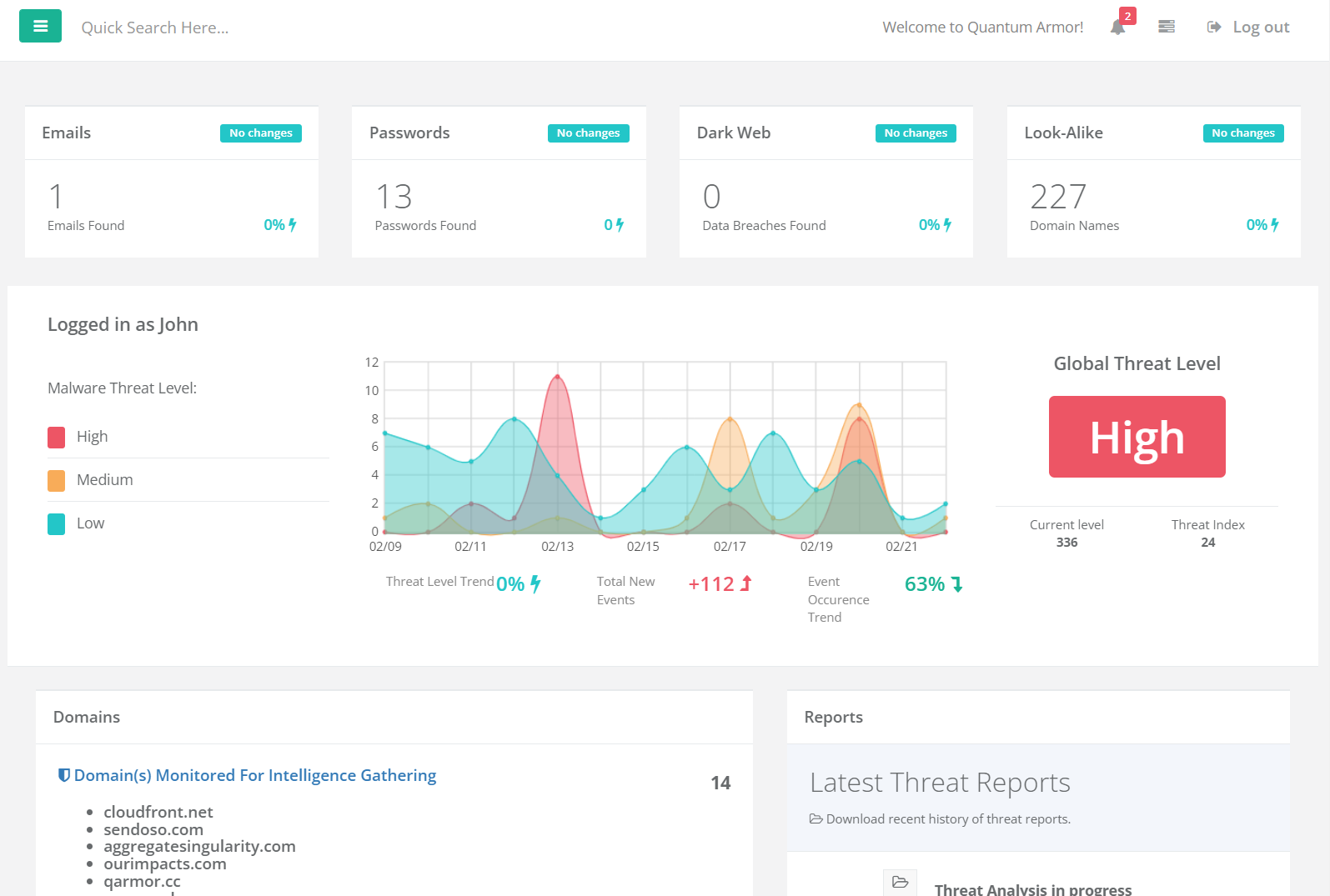
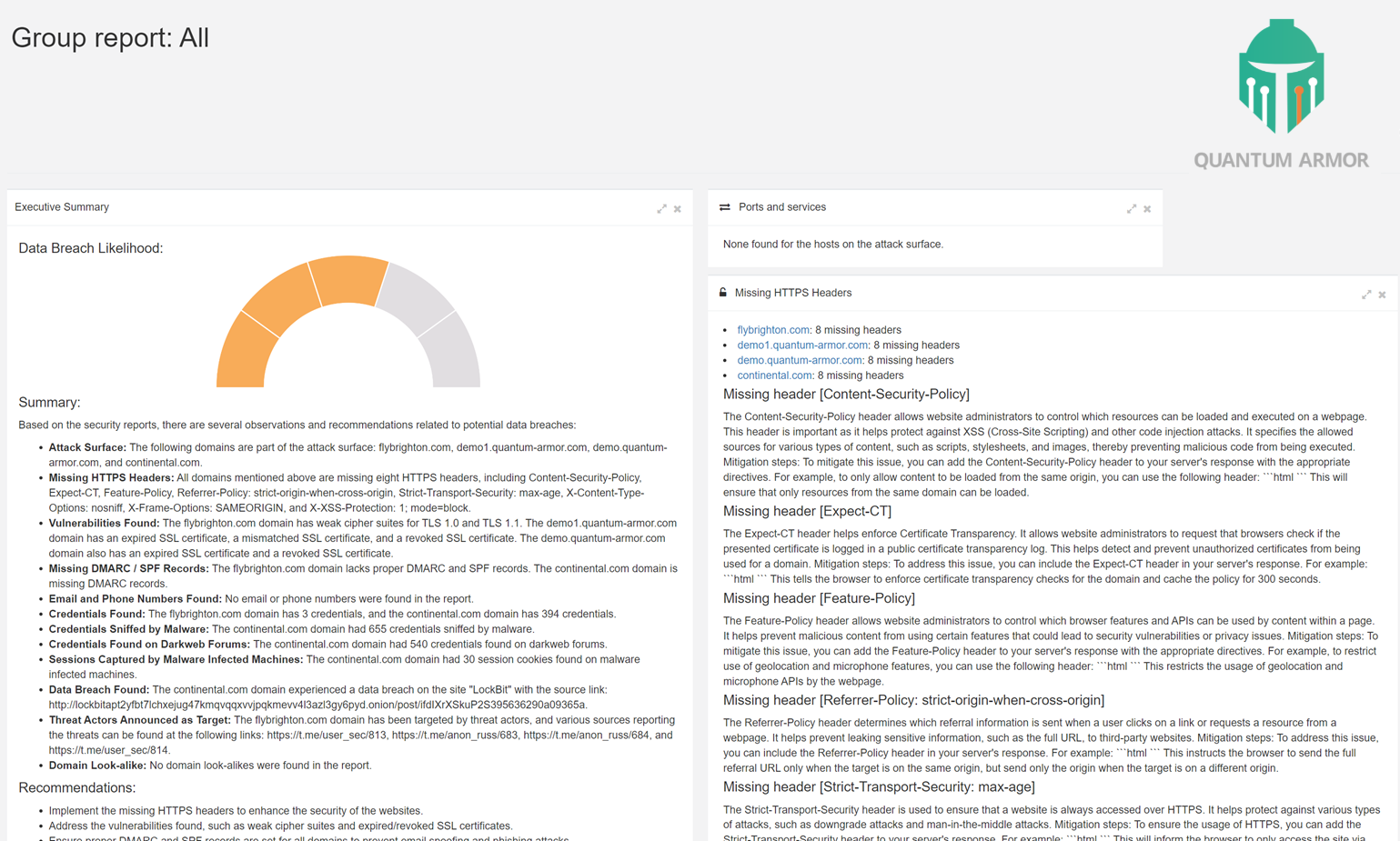
The Quantum Armor LLM ingests thousands of data points and provides a daily security brief including an executive summary, security rating, detailed findings, and recommended roadmap along with the likelihood of an imminent data breach.
Learn More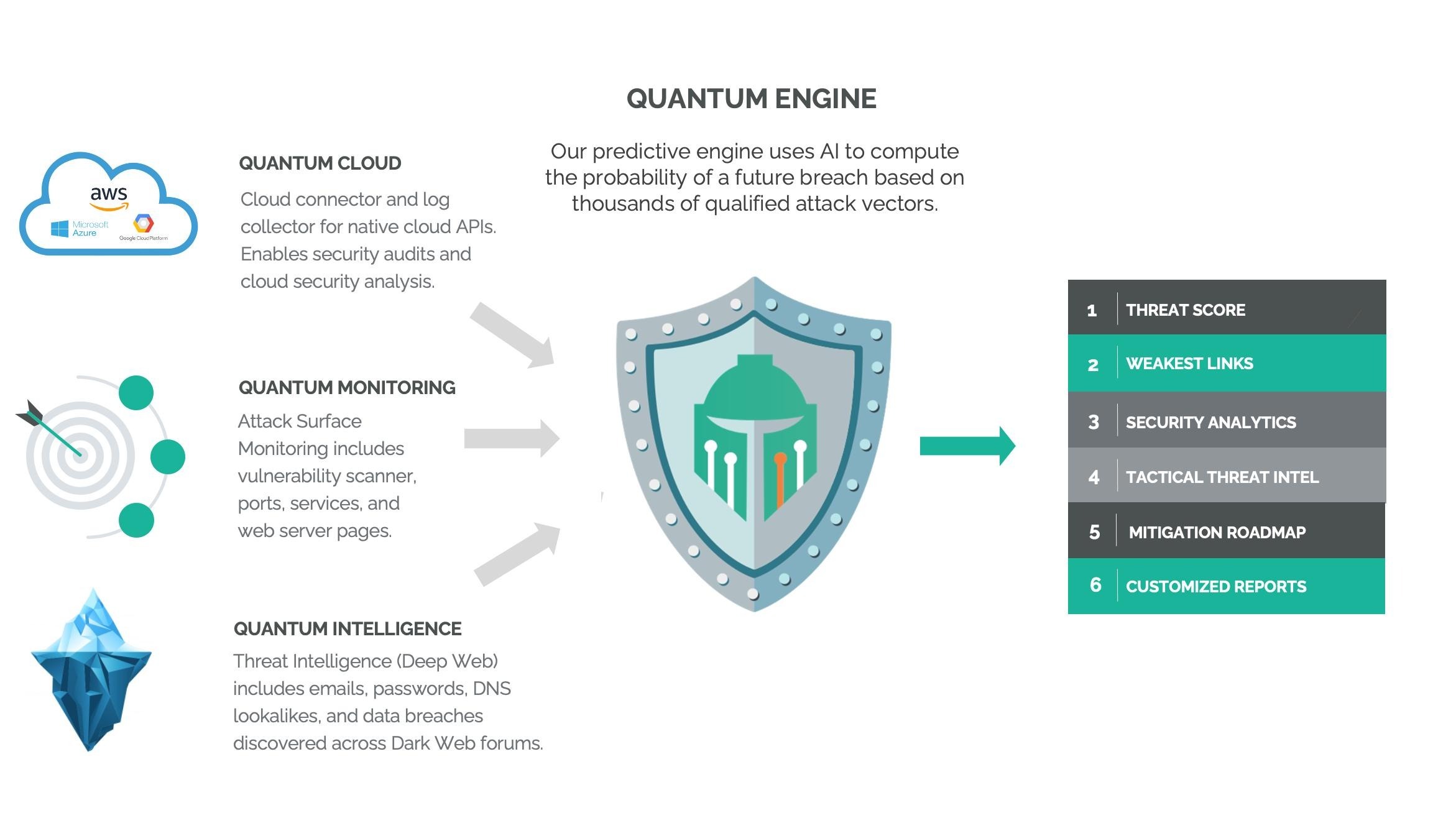
Flexible plans to suit your needs.
*MSP/MSSP pricing available, click here for more details.
Quantum Armor™ is a Silent Breach product.
Silent Breach is a leading cybersecurity firm specializing in network security and digital asset protection.
Please visit https://silentbreach.com to learn more.
Follow us on social media
© Silent Breach
Quantum Armor micro-site. Please visit https://silentbreach.com for more information on Silent Breach.